Checkpoint
Cyber Security Solutions for the Modern-Day Workplace
 As more and more enterprises move their operations to the digital world, the world of cyber security continues to grow to meet their diverse needs. Tazcom takes the lead by partnering with software development companies providing innovative solutions – to help create and maintain a secure IT environment for your business.
As more and more enterprises move their operations to the digital world, the world of cyber security continues to grow to meet their diverse needs. Tazcom takes the lead by partnering with software development companies providing innovative solutions – to help create and maintain a secure IT environment for your business.
Predict, detect, and avert cyber attacks with advanced cyber security solutions from Tazcom!
We are an authorised partner of Checkpoint and offer a range of its innovative cyber security products to help you build safe digital spaces.
Protecting Businesses in the Digital World
The prevalence of remote and hybrid workplaces has increased dramatically within the past few years (especially after the COVID-19 pandemic), and so have the threats to them. As businesses find newer ways to conduct their operations online, cybercrimes are also evolving, posing newfangled risks for disruptive digital attacks.
 Tazcom responds to this rapidly changing cyber-security scenario by providing innovative protective software systems. Checkpoint’s advanced security solutions can avert even the most sophisticated cyber-attacks, ensuring your system and data remain safe from malicious attempts. Checkpoint takes security solutions seriously and was also the company who gave us the 1st firewall.
Tazcom responds to this rapidly changing cyber-security scenario by providing innovative protective software systems. Checkpoint’s advanced security solutions can avert even the most sophisticated cyber-attacks, ensuring your system and data remain safe from malicious attempts. Checkpoint takes security solutions seriously and was also the company who gave us the 1st firewall.
Take the first step to secure your digital workspace today. Contact us to find a suitable cybersecurity solution for your enterprise.
Diverse Solutions for Versatile Workplaces
No two businesses are the same. Even if they are operating in the same industry and providing similar products or services, every company is distinct and different from its peers and competitors in more ways than one. This makes universal cyber security systems an obsolete concept. At Tazcom, we do not believe in a one-size-fits-all approach. Therefore, we offer a broad range of security solutions catering to the diverse needs of enterprises in today’s rapidly evolving digital space.
Check out our product catalogue to choose the best digital security solution for your company.
Assess and Avert Cyber Security Threats with Tazcom
 Don’t wait for the black hat hackers to attack your system to launch a response. Build a strong, comprehensive security system that’s impenetrable to avert the risks in the first place.
Don’t wait for the black hat hackers to attack your system to launch a response. Build a strong, comprehensive security system that’s impenetrable to avert the risks in the first place.
Assess, test, and strengthen your cyber security across all digital vectors with us.
Start with a free cyber security risk assessment!
Our cyber security risk assessment is a comprehensive evaluation, testing, and analysis of your IT system to identify the security loopholes that hackers can potentially take advantage of. Take the first step to keeping your information and processes safe from intruders.
The Cyber Security Solutions We Offer
We at Tazcom offer a wide range of digital security software and systems to help diverse types of businesses meet their unique cybersecurity needs. However, Checkpoint’s innovative solutions we have can be grouped into four major categories.

Quantum
Prized for its scalability, this advanced network protection system provides the best security gateways to prevent the most calculated and strongest cyber attacks.

Cloud Guard
With statistics showing that most businesses now use cloud platforms to communicate, cooperate, work, and store data, there’s a strong need for them to invest in advanced cloud security solutions to keep their virtual workspaces and data safe from attackers. Our Cloud Guard checks the box as no other solution does.

Harmony
Allow your diverse workforce to work from wherever they want without compromising their security or your data. Build secure user access across multiple platforms with our Harmony solutions.

Horizon
Convert your reactive cyber security to a proactive approach with our state-of-the-art threat detection and prevention tools.
Want an All-Inclusive Solution? Avail Check Point Infinity Global Services
Check Point Infinity Global Services is a comprehensive digital security solution that provides end-to-end cyber security services to prevent advanced threats, respond to attacks, and improve security resilience strategy.


 Tazcom is the authorized reseller of Spectralink mobile communication products that are secure and cost-effective. Spectralink delivers mobility to enterprises from various industries, allowing your employees to collaborate and communicate anywhere, anytime. Better workers, greater revenue!
Tazcom is the authorized reseller of Spectralink mobile communication products that are secure and cost-effective. Spectralink delivers mobility to enterprises from various industries, allowing your employees to collaborate and communicate anywhere, anytime. Better workers, greater revenue! Mobile communications have become integral to business in today’s digital era. 80% of the world’s staff is mobile. An increasingly hybrid workplace has mandated the need for better communication methods that keep both desk-based and remote employees connected at all times. Traditional means of communication, like bulletin boards, are outdated relics, and mobile-first communications have become mainstream due to quicker exchange.
Mobile communications have become integral to business in today’s digital era. 80% of the world’s staff is mobile. An increasingly hybrid workplace has mandated the need for better communication methods that keep both desk-based and remote employees connected at all times. Traditional means of communication, like bulletin boards, are outdated relics, and mobile-first communications have become mainstream due to quicker exchange.

 Spectralink wireless headsets eliminate paging delays to improve delivery time and ensure quicker emergency response time
Spectralink wireless headsets eliminate paging delays to improve delivery time and ensure quicker emergency response time
 Tazcom is known for providing unified communications (UC) products and solutions under one domain. Ascom has healthcare and enterprise platforms for higher productivity, safety, and enhanced customer satisfaction. Their product portfolio services various industries, including healthcare, retail, industry, and hospitality. Fulfil all your communication needs here.
Tazcom is known for providing unified communications (UC) products and solutions under one domain. Ascom has healthcare and enterprise platforms for higher productivity, safety, and enhanced customer satisfaction. Their product portfolio services various industries, including healthcare, retail, industry, and hospitality. Fulfil all your communication needs here. Workflow integration is central to the success of any business or industry. It ensures greater efficiency among various workflow processes, mitigating IT work and costs. This allows companies to reduce labour costs and boost workplace revenue. Ascom’s integrated workflow solution allows workflow automation, reducing the time and energy staff (especially in hospitals) spend on repetitive tasks. This improves employee motivation and hence, productivity.
Workflow integration is central to the success of any business or industry. It ensures greater efficiency among various workflow processes, mitigating IT work and costs. This allows companies to reduce labour costs and boost workplace revenue. Ascom’s integrated workflow solution allows workflow automation, reducing the time and energy staff (especially in hospitals) spend on repetitive tasks. This improves employee motivation and hence, productivity.






 Effective communication throughout the business is integral as it enhances the satisfaction, productivity, engagement, and morale of the employees. Communication also plays a significant role in improving cooperation and collaboration between teams.
Effective communication throughout the business is integral as it enhances the satisfaction, productivity, engagement, and morale of the employees. Communication also plays a significant role in improving cooperation and collaboration between teams.



 Poly has extensive experience of over 50 years of creating premium audio and video solutions that allow you to have the best meeting. See fewer interruptions and roadblocks when working from home, which impedes effective remote work. Poly is all about an immersive experience, which is the need in today’s digital age.
Poly has extensive experience of over 50 years of creating premium audio and video solutions that allow you to have the best meeting. See fewer interruptions and roadblocks when working from home, which impedes effective remote work. Poly is all about an immersive experience, which is the need in today’s digital age. Communication was always integral to the success of any business. Whether you need to interact with clients or employees, you need effective tools of communication. With many substandard products in the market, Poly’s professional-grade equipment ensures effective collaboration throughout the organization. It provides Microsoft Teams, Zoom and Office Workplace solutions. The benefits of this are endless, some of which include employee flexibility and clear communication from anywhere, anytime.
Communication was always integral to the success of any business. Whether you need to interact with clients or employees, you need effective tools of communication. With many substandard products in the market, Poly’s professional-grade equipment ensures effective collaboration throughout the organization. It provides Microsoft Teams, Zoom and Office Workplace solutions. The benefits of this are endless, some of which include employee flexibility and clear communication from anywhere, anytime.
 A wide range of high-tech headsets to suit every business’s needs
A wide range of high-tech headsets to suit every business’s needs
 The Tazcom team has over 25 years of experience providing Unified Communications (UC) products and services from industry-leading vendors. We allow voice and video integration into existing infrastructure, without the transacting hassle. With increasing competition, seamless communication and collaboration are at the heart of any successful business. At Tazcom, we aim to bring you the best solutions that ensure enhanced workplace productivity.
The Tazcom team has over 25 years of experience providing Unified Communications (UC) products and services from industry-leading vendors. We allow voice and video integration into existing infrastructure, without the transacting hassle. With increasing competition, seamless communication and collaboration are at the heart of any successful business. At Tazcom, we aim to bring you the best solutions that ensure enhanced workplace productivity. The up-and-coming business generation is all about voice and video c
The up-and-coming business generation is all about voice and video c



 Cisco is a prominent name, providing technology to businesses. Cisco acquired Broadsoft in 2018, owing to its commitment to Unified Communications (UC). The company boasts a vast portfolio consisting of audio solutions, WebEx services, Cloud UC-One SaaS solutions, and network connectivity solutions. Since its acquisition of Broadsoft, clients have an even greater range of products to suit every type of business.
Cisco is a prominent name, providing technology to businesses. Cisco acquired Broadsoft in 2018, owing to its commitment to Unified Communications (UC). The company boasts a vast portfolio consisting of audio solutions, WebEx services, Cloud UC-One SaaS solutions, and network connectivity solutions. Since its acquisition of Broadsoft, clients have an even greater range of products to suit every type of business. Cisco is the leading provider of technology products that make business operations easier. Tazcom chose Cisco for its Unified Communications portfolio, which integrates various aspects to create a successful system of crucial business processes, people, and technology. Cisco is known for its innovation, coming up with new solutions to meet the changing business landscape needs. Cisco is up-to-date with the switch to a hybrid workplace, allowing you various channels and ways to intercut with employees, wherever they may be.
Cisco is the leading provider of technology products that make business operations easier. Tazcom chose Cisco for its Unified Communications portfolio, which integrates various aspects to create a successful system of crucial business processes, people, and technology. Cisco is known for its innovation, coming up with new solutions to meet the changing business landscape needs. Cisco is up-to-date with the switch to a hybrid workplace, allowing you various channels and ways to intercut with employees, wherever they may be.
 It is no hidden fact that the pandemic has changed the way we work. There has been a significant shift towards remote work, which mandates the need for a cloud strategy and collaboration, both of which Cisco provides. Cisco collaboration helps businesses achieve their goals, whether it’s to streamline operations, make faster decisions, and save resources.
It is no hidden fact that the pandemic has changed the way we work. There has been a significant shift towards remote work, which mandates the need for a cloud strategy and collaboration, both of which Cisco provides. Cisco collaboration helps businesses achieve their goals, whether it’s to streamline operations, make faster decisions, and save resources.

 Tazcom is dedicated to providing unrivalled products in the world of Unified Communications. We bring customers products from the cream of technology providers like Ribbon Communications. Since its inception and over two decades of experience, Ribbon has quickly become a trusted choice for customers worldwide.
Tazcom is dedicated to providing unrivalled products in the world of Unified Communications. We bring customers products from the cream of technology providers like Ribbon Communications. Since its inception and over two decades of experience, Ribbon has quickly become a trusted choice for customers worldwide.
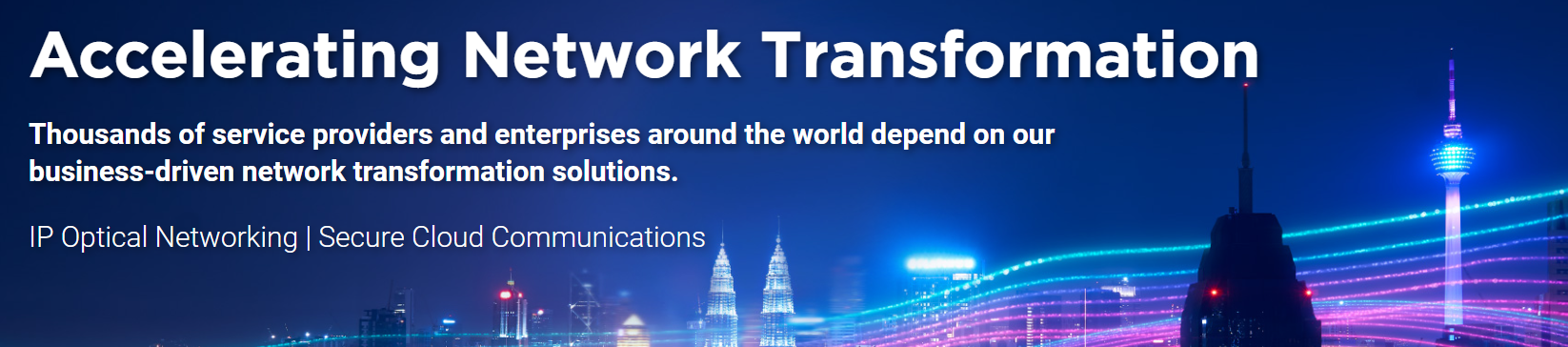
 Ribbon Communications offers IP optical networking and secure cloud communications services to deliver network transformation to enterprises all over the world. In today’s data-hungry world, delivering fast solutions is the primary aim of every business. Whether you want to transfer from a Primary Rate Interface (PRI) line to a VoIP or adopt a cloud-native application, Ribbon has the right product portfolio for each.
Ribbon Communications offers IP optical networking and secure cloud communications services to deliver network transformation to enterprises all over the world. In today’s data-hungry world, delivering fast solutions is the primary aim of every business. Whether you want to transfer from a Primary Rate Interface (PRI) line to a VoIP or adopt a cloud-native application, Ribbon has the right product portfolio for each.
 Tazcom is the authorized reseller and distributor of Unified Communications (UC) products and solutions from industry leaders like Video Window. Video conferencing has remained an integral part of the remote business landscape for as long as we can remember. With increasing innovation and technological advances, businesses can now adopt an even more streamlined version of the traditional video conferencing system.
Tazcom is the authorized reseller and distributor of Unified Communications (UC) products and solutions from industry leaders like Video Window. Video conferencing has remained an integral part of the remote business landscape for as long as we can remember. With increasing innovation and technological advances, businesses can now adopt an even more streamlined version of the traditional video conferencing system.
 The office culture has a direct impact on a company’s productivity, as well as the power to hire and retain the best employees. Video Window understands this challenge facing today’s businesses, especially with the increasing hybrid workplace trend following Covid.
The office culture has a direct impact on a company’s productivity, as well as the power to hire and retain the best employees. Video Window understands this challenge facing today’s businesses, especially with the increasing hybrid workplace trend following Covid. Businesses might wonder, we have video conferencing; does it really need to be always-on, literally? The current findings show that it is highly beneficial. In today’s age, workplace productivity is driven by employee engagement and team spirit more than anything else.
Businesses might wonder, we have video conferencing; does it really need to be always-on, literally? The current findings show that it is highly beneficial. In today’s age, workplace productivity is driven by employee engagement and team spirit more than anything else.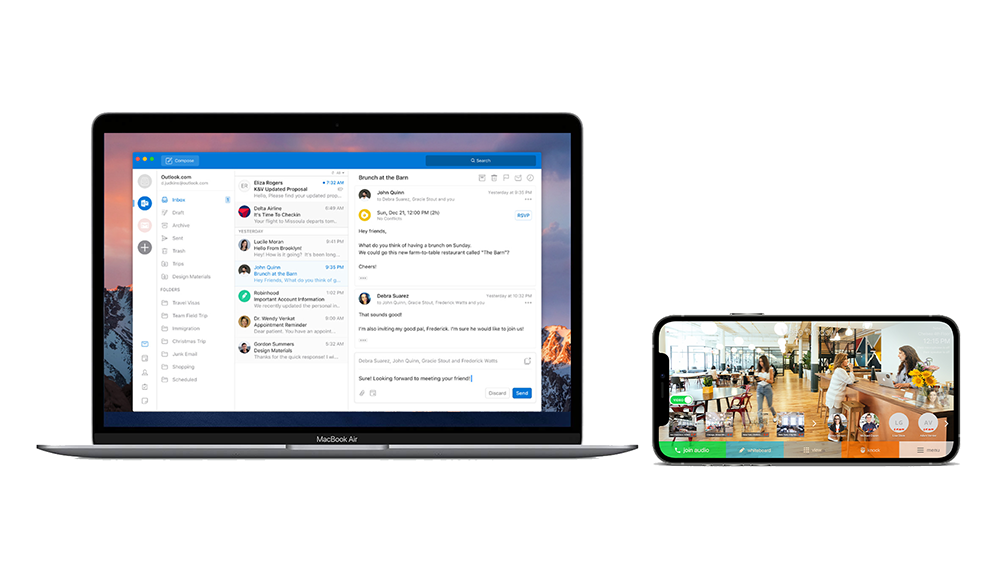


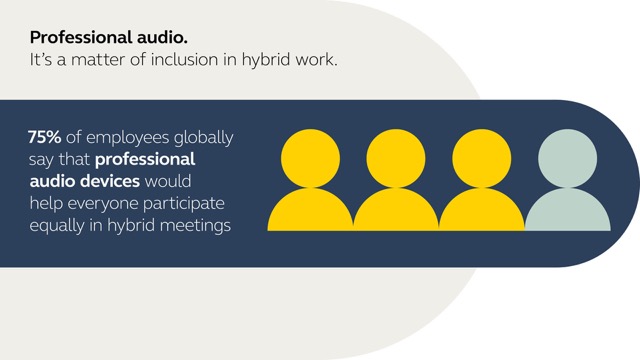






 Communication is an imperative part of any business. It has become even more vital with the increase in hybrid work. However, most employees don’t have the right equipment to participate fully. When you have the right technology like Jabra’s headsets and conference devices, the whole world is practically your workspace! Communicate with employees and clients anywhere in the world with fewer interruptions and nuisances.
Communication is an imperative part of any business. It has become even more vital with the increase in hybrid work. However, most employees don’t have the right equipment to participate fully. When you have the right technology like Jabra’s headsets and conference devices, the whole world is practically your workspace! Communicate with employees and clients anywhere in the world with fewer interruptions and nuisances.